As reported in Technology Decisions, 68% of all reported data breaches in 2016 were linked to malicious outsiders. And the volume of records exposed by those outsiders surged by 286% over 2015 volume, according to the Breach Level Index published by Gemalto. The report was released a few months ago, but trawling back over the
We thought it might be interesting to let you take a peek behind the curtains at what Computer One is working on right now for a selection of clients. We find the diversity of the challenges quite exciting! Keeping Pace with a Mine Site in Northwestern QLD We’ve been on the ground at a outside
When was the last time you got help with your strategic planning in IT? “What?” you say. “Strategic plans are for the sales and marketing team and the executive retreat. Our IT team is there to help us keep the lights on and maintain business-as-usual conditions. When they want to upgrade a system they put
We’re proud to announce the opening of our NSW office in the heart of Sydney’s CBD at 133 Castlereagh Street. Having served our southern clients for more than a decade from our Brisbane office, our new presence adds a local touch to our nationwide scope and comes in the wake of an increasing number of
A new report by Verizon continues to confirm that the human is the weakest link in any network security chain. The Verizon Enterprise 2017 Data Breach Digest contains numerous accounts of real-life stories of data breaches, corporate theft, million-dollar scams and emergency responses to contain and remedy the situations. The document presents some key metrics
Just yesterday, the Federal Government passed an amendment to the Privacy Act that requires organisations with turnover of $3m or more to publicly disclose they’ve suffered a data breach with respect to personal information of clients, employees, research participants and more. The change comes after 4 years of trying to get an amendment passed, with
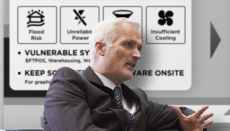
Last week it emerged that 3 out of a group of 4 health services whose disaster recovery preparations have been assessed by the Queensland Audit Office have only basic DR measures in place. Computerworld reports that Cairns, Mackay and South West Hospitals and Health Services only scored a 1 on the capability maturity model used
Ransomware attacks have quadrupled in the past year because companies like yours are paying up! A report released by insurance underwriter Beazley last week found the lure of an easy pay-day, combined with the ease of buying easy-to-operate ransomware kits, had made the attacks a real growth industry for cyber-criminals. “From what we are seeing,
Digital video recorders (DVRs) and IP cameras were the unlikely weapons of a global cyber-attack that brought one of the internet’s biggest players to its knees. The distributed denial of service (DDoS) attack against US domain name server (DNS) provider Dyn occurred late last week [October 22]. It caused congestion, and service outages to many
Hackers are now increasingly targeting attacks at small to mid-range enterprises. Why? Because it’s easy, and it gives cyber-criminals a better chance of infiltrating other bigger networks – including those of your clients – using your circle of trust. That’s just one of the findings released in the latest Australian Cyber Security Centre (ACSC) threat
As published in IT News, a business in South Australia has been relieved of $1,500,000 as the result of a concentrated yet straightforward fraud operation run by overseas attackers. Two other companies have also been targeted to the value of more than $400,000 but those funds were prevented from leaving the country. South Australian police
Hackers can now use your own employees’ smartphones against you to launch digital espionage attacks, and hijack sensitive corporate information using a Trojan horse called DressCode. Security specialists Trend Micro report the malware allows hackers to bypass your Firewalls by accessing connected internal networks through the compromised device, which are already beyond the router. It
We’re pleased to announce that we can now develop custom software and business reporting tools for your company. We have expanded our range of products and services based on market feedback from our clients that they need to innovate and become more agile with the help of IT. Our new team members are experienced programmers
As reported in IT News, malware that has a very specific purpose has been found lurking in the Google Play store. It’s called Overseer, and it’s designed to target business travellers going overseas. It steals lots of information for a very specific purpose. Once installed on a user’s Android device, Overseer collects and sends back
In IT Security, two industry terms deserve a bit of explaining. They are: What is an Attack Vector? An “Attack Vector” is the IT industry’s term for describing the path that a hacker or a malware application might follow to infiltrate your IT network and compromise your data. Attack Vectors exploit systemic vulnerabilities and human